
When Your Guard Dog Bites: Understanding the BlueHammer Zero-Day in Microsoft Defender
By M. SiddiqBaig | pentestersiddiq.com | April 23, 2026
Imagine your home’s security system—the one you trust to keep intruders out—suddenly being used to unlock the front door for a burglar. That’s not a hypothetical. It’s exactly what’s happening with “BlueHammer,” a newly discovered zero-day vulnerability (CVE-2026-33825) and CWE-1220: CWE-1220: Insufficient Granularity of Access Control in Microsoft Defender.
Instead of stopping threats, this flaw allows attackers to weaponize the antivirus engine itself. With just low-level access, an attacker can escalate privileges all the way to SYSTEM—the highest level on Windows. And yes, this isn’t theoretical anymore. It’s already being exploited in the wild.
At its core, BlueHammer (tracked as CVE-2026-33825) is a local privilege escalation (LPE vulnerability is a security flaw that allows a user with low-level access (such as a standard user or guest) to gain higher-level permissions (e.g., administrator, root, or SYSTEM) on a system. Synonyms include privilege elevation attack, vertical privilege escalation, or privilege escalation exploit). It doesn’t let attackers break in remotely—but once they’re inside, it gives them the keys to the kingdom.
Here’s what makes it tick:
In plain terms: the system checks something… and before it acts on it, an attacker swaps it out. That tiny timing gap is all it takes.
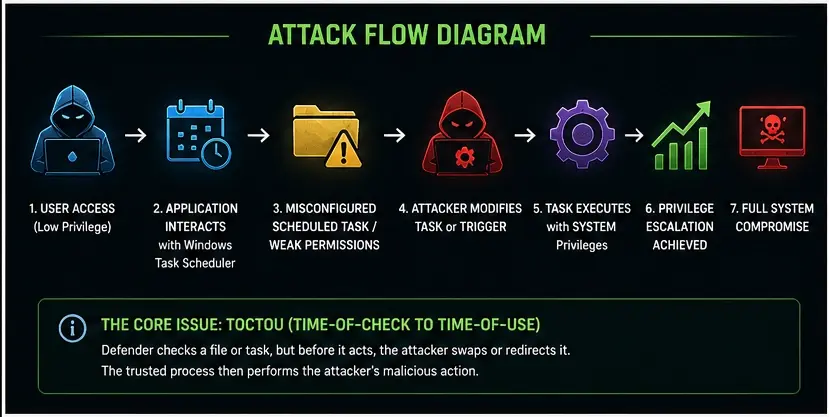
Let’s simplify what’s happening behind the scenes.
The attacker places a file that looks malicious on the system—something that will trigger Defender.
Defender detects the file and prepares to delete or quarantine it.
In that split second between detection and action, the attacker redirects the operation using symbolic links or junctions.
Defender—running with high privileges—ends up overwriting critical system files (like those in C:\Windows\System32) with malicious code.
The attacker now has SYSTEM-level control.
The clever (and scary) part? This entire operation is executed by a trusted security process (MsMpEng.exe). To many defences, it looks legitimate.
This isn’t just another theoretical CVE sitting in a database.
A lot of vulnerabilities attack from the outside. BlueHammer is different—it attacks trust.
This is what security teams often call a “double-edged sword” vulnerability (a technology, tool, or strategy that offers significant defensive benefits while simultaneously creating equally powerful opportunities for abuse by attackers.
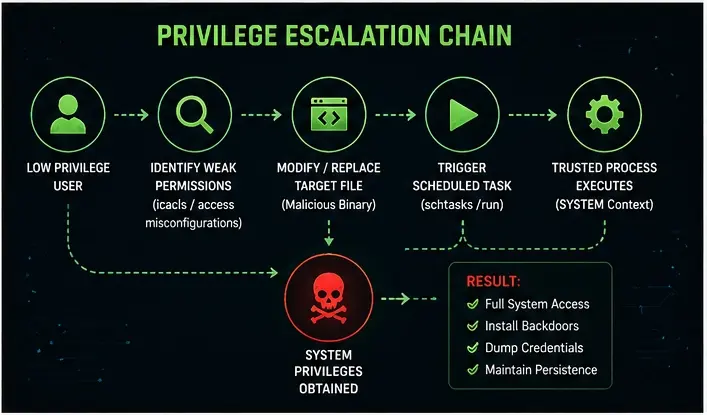
# Enumerate scheduled tasks
schtasks /query /fo LIST /v
# Identify weak permissions
icacls "C:\Path\To\Executable.exe"
# Replace binary
copy malicious.exe target.exe
# Execute task
schtasks /run /tn "TaskName"
# SYSTEM shell
whoami
Microsoft released a fix during the April 14, 2026 Patch Tuesday.
Make sure you’re running an updated Microsoft Malware Protection Engine (April 2026 release or later).
Don’t rely on signatures alone:
Monitor for:
Since this is an LPE vulnerability:
In cybersecurity, the biggest threats aren’t always zero-days — sometimes they’re simple misconfigurations waiting to be abused.
If you manage endpoints, here’s your action plan:
Conclusion BlueHammer highlights a dangerous reality: even trusted security tools can be abused. A simple race condition combined with weak permissions can lead to full system compromise.
A critical privilege escalation vulnerability (CVE-2026-33825) that exploits a race condition in Microsoft Defender to gain SYSTEM access.
Yes. As of April 23, 2026, active exploitation has been confirmed, and CISA has flagged it as high priority.
Yes—verify the update actually applied. Don’t rely on assumptions.
No. It requires local access—but once inside, it’s extremely powerful.